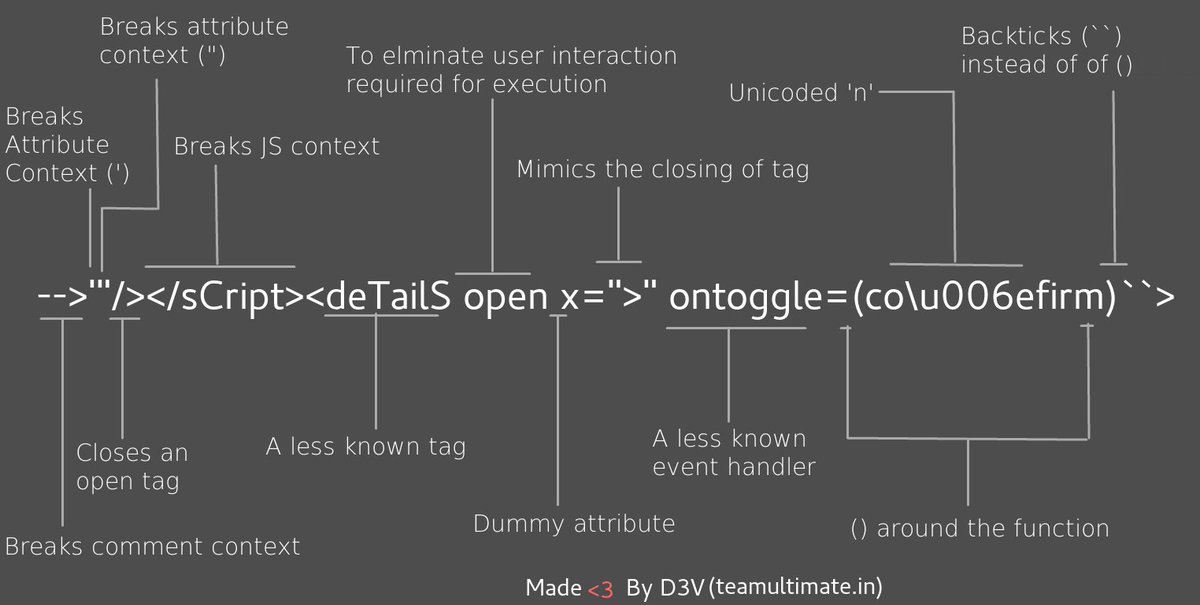
This cross-site scripting (XSS) cheat sheet contains many vectors that can help you bypass WAFs and filters. You can select vectors by the event, tag or browser and a proof of concept is included for every vector. You can download a PDF version of the XSS cheat sheet. This cheat sheet was brought to by PortSwigger Research. XSS filter evasion refers to a variety of methods used by attackers to bypass XSS (Cross-Site Scripting) filters. There are many ways to inject malicious JavaScript into web page code executed by the client, and with modern browsers, attackers must not only exploit an application vulnerability but also evade any input validation performed by the application and server, and fool complex browser. Execution Hacks v1.0 XSS Payloads www.xss-payloads.com Function Example Synopsis Function('alert(1)') Function(') self(typeof prompt. For a cheatsheet on the attack vectors related to XSS, please refer to the XSS Filter Evasion Cheat Sheet. More background on browser security and the various browsers can be found in the Browser Security Handbook. Before reading this cheatsheet, it is important to have a fundamental understanding of Injection Theory.
Xss Payload Cheat Sheet Pdf
XSS Payload Cheat Sheet. Contribute to rootbakar/XSS-Payload development by creating an account on GitHub.
| 🔥Complete Bug Bounty Cheat Sheet🔥 |
| XSS |
| https://github.com/EdOverflow/bugbounty-cheatsheet/blob/master/cheatsheets/xss.md |
| https://github.com/ismailtasdelen/xss-payload-list |
| SQLi |
| https://github.com/EdOverflow/bugbounty-cheatsheet/blob/master/cheatsheets/sqli.md |
| SSRF |
| https://github.com/EdOverflow/bugbounty-cheatsheet/blob/master/cheatsheets/ssrf.md |
| https://github.com/swisskyrepo/PayloadsAllTheThings/tree/master/Server%20Side%20Request%20Forgery |
| CRLF |
| https://github.com/EdOverflow/bugbounty-cheatsheet/blob/master/cheatsheets/crlf.md |
| https://github.com/swisskyrepo/PayloadsAllTheThings/tree/master/CRLF%20Injection |
| CSV-Injection |
| https://github.com/EdOverflow/bugbounty-cheatsheet/blob/master/cheatsheets/csv-injection.md |
| https://github.com/swisskyrepo/PayloadsAllTheThings/tree/master/CSV%20Injection |
| Command Injection |
| https://github.com/swisskyrepo/PayloadsAllTheThings/tree/master/Command%20Injection |
| Directory Traversal |
| https://github.com/swisskyrepo/PayloadsAllTheThings/tree/master/Directory%20Traversal |
| LFI |
| https://github.com/EdOverflow/bugbounty-cheatsheet/blob/master/cheatsheets/lfi.md |
| https://github.com/swisskyrepo/PayloadsAllTheThings/tree/master/File%20Inclusion |
| XXE |
| https://github.com/EdOverflow/bugbounty-cheatsheet/blob/master/cheatsheets/xxe.md |
| Open-Redirect |
| https://github.com/EdOverflow/bugbounty-cheatsheet/blob/master/cheatsheets/open-redirect.md |
| RCE |
| https://github.com/EdOverflow/bugbounty-cheatsheet/blob/master/cheatsheets/rce.md |
| Crypto |
| https://github.com/EdOverflow/bugbounty-cheatsheet/blob/master/cheatsheets/crypto.md |
| Template Injection |
| https://github.com/EdOverflow/bugbounty-cheatsheet/blob/master/cheatsheets/template-injection.md |
| https://github.com/swisskyrepo/PayloadsAllTheThings/tree/master/Server%20Side%20Template%20Injection |
| XSLT |
| https://github.com/EdOverflow/bugbounty-cheatsheet/blob/master/cheatsheets/xslt.md |
| Content Injection |
| https://github.com/EdOverflow/bugbounty-cheatsheet/blob/master/cheatsheets/content-injection.md |
| LDAP Injection |
| https://github.com/swisskyrepo/PayloadsAllTheThings/tree/master/LDAP%20Injection |
| NoSQL Injection |
| https://github.com/swisskyrepo/PayloadsAllTheThings/tree/master/NoSQL%20Injection |
| CSRF Injection |
| https://github.com/swisskyrepo/PayloadsAllTheThings/tree/master/CSRF%20Injection |
| GraphQL Injection |
| https://github.com/swisskyrepo/PayloadsAllTheThings/tree/master/GraphQL%20Injection |
| IDOR |
| https://github.com/swisskyrepo/PayloadsAllTheThings/tree/master/Insecure%20Direct%20Object%20References |
| ISCM |
| https://github.com/swisskyrepo/PayloadsAllTheThings/tree/master/Insecure%20Source%20Code%20Management |
| LaTex Injection |
| https://github.com/swisskyrepo/PayloadsAllTheThings/tree/master/LaTeX%20Injection |
| OAuth |
| https://github.com/swisskyrepo/PayloadsAllTheThings/tree/master/OAuth |
| XPATH Injection |
| https://github.com/swisskyrepo/PayloadsAllTheThings/tree/master/XPATH%20Injection |
| Bypass Upload Tricky |
| https://github.com/swisskyrepo/PayloadsAllTheThings/tree/master/Upload%20Insecure%20Files |
| BURP |
| https://drive.google.com/file/d/1r1LGt7fEh8AuhihrBfp1GGmU9ttV9CkP/view?usp=sharing |
| https://drive.google.com/file/d/1IOgrVUIQb9HGQG9tePe3v_w2gyaymUFq/view?usp=sharing |

The Book takes care to explain the elevation of Cross-Site Scripting (XSS) to the title of HTML Injection. This quick reference describes some of the common techniques used to inject a payload into a web application.
In the examples below the biohazard symbol (U+2623), ☣, represents an executable JavaScript payload. It could be anything from a while loop to lock the browser, e.g. while(1){a=1;}, or something more useful that a creative attacker comes up with. You can quite easily find “XSS Cheat Sheets” elsewhere. The intent of this reference is to instill a sense of methodology into finding HTML injection vulnerabilities. Good exploits take advantage of HTML syntax and browser quirks in creative ways. Take the time to experiment with simple payloads and observe how (and where) the web application reflects them. Then turn towards the list of complex attacks on a cheat sheet.
Also notice how the syntax of elements and JavaScript have been preserved in cases where single- or double-quotes are used to prefix a payload. The injected quote prematurely ends a quoted string, which means there will be a dangling quote at the end. Whether the reflection point is in an intrinsic event or a JavaScript block, the dangling quote is trivially consumed by throwing an extra variable definition with an open quote:
Parallels app for mac. ;a='
The dangling quote will close the delimiter and, in most cases, the syntax will be preserved. This type of closure isn’t really necessary for an exploit to work, but it’s a sign craftier exploits.
The table’s layout is a bit constrained by the format of this post. Keep an eye on it for updates to content as well as presentation.
Xss Payloads List

Xss Injection Cheat Sheet
table { border-collapse: collapse; border: solid }thead { border: solid medium; text-align: center; }td { border: solid thin; text-align: center; padding: 2px; }.leftText { text-align: left }
| Technique | Characters | Payload Example | Injection Example |
|---|---|---|---|
| Close a start tag in order to insert a new element (This usually happens within an element attribute, but keep in mind HTML comments and XML CDATA.) | > /> –> ]]> | ><script>☣<script> | <input type=text name=id value= ><script>☣<script> > |
| Insert an end tag in order to insert a new element (Also useful where XML appears, such as RSS feeds.) | </element> ]]> | ]]><script>☣<script> | <INFO><![CDATA[ ]]><script>☣</script> |
| Close a quoted attribute in order to insert an intrinsic event | ” (ASCII 0x22) ‘ (ASCII 0x27) | “onEvent=☣;a=” | <a href=”/redir?url=http://” onClick=☣;a=”“> |
| Break out of a JavaScript variable | ” (ASCII 0x22) ‘ (ASCII 0x27) | “;{☣}var foo=” | <script> var host = window.location; var lastLink = “http://web.site/index?refurl=“;{☣}var foo=”“; … <script> |
| Split payload across multiple reflection points (Also a good way to bypass filters. Use HTML comment delimiters to elide content between the two payloads. In some cases you might be able to use quoted strings to elide content.) | (as above) | 1: “<script<!– 2: –>>☣</script> | <input value=”“<script<!– “>other content <input value=” –>>☣</script>“ |
| Alter MIME interpretation of uploaded file (Usually when content is expected to be served as text/plain, binary, or other non-HTML type) | Must be able to influence Content-Type header or browser’s MIME sniffing algorithm | text/html application/x-javascript | Uploaded file contains JavaScript. Image EXIF data contains HTML & JavaScript. |
| Bypass a filter using browser quirk | Alternate whitespace character Non-standard element or attribute | – | See http://x86.cx/html5/ for an example of a complex src attribute for an img element. |
| Bypass a filter using alternate or invalid character encoding (The goal is to find a sequence that disrupts or confuses a parser enough that a character such as ASCII 0x22 is considered part of a multibyte sequence, but is served to the browser as a single-byte character. This would either occur because a server-side filter incorrectly stripped or rewrote the invalid sequence or the browser’s character parser misinterpreted the sequence.) | UTF-7 UTF-8 Unicode | – | %fe%22 %fd%22 %cd%22 %c1%22 %c0%a2 %80%22 %22 |
| JavaScript execution in CSS and style definitions [Obsolete for modern browsers due to security concerns] | – | – | IE Expressions Mozilla -moz-binding |
